Microsoft Cloud App Security
Microsoft Defender For Cloud Apps is a cloud access security broker (CASB) that supports various deployment modes, including log collection, API connectors, and reverse proxy. It provides rich visibility, data travel control and sophisticated analytics to identify and combat cyber threats across all Microsoft and other cloud services.
Microsoft Defender for Cloud Apps integrates smoothly with leading Microsoft solutions and is designed with security professionals in mind. It provides simple deployment, centralized management, and innovative automation capabilities.
Why MCAS?
The need for CASB is to better understand your overall cloud posture in SaaS applications and cloud services, Shadow IT detection and application management are examples of key use cases. In addition, the organization is responsible for managing and securing its cloud platform including IAM, VMs and its computing resources, data and storage, network resources and more. So, if you’re an organization that uses, or is considering using cloud applications for your portfolio of network services, you likely need a CASB to address the additional and unique challenges of regulating and securing your environment. For example, there are many ways for malicious actors to leverage cloud applications to enter your corporate network and extract sensitive business data.
As an organization, you need to protect your users and confidential data from the various methods employed by malicious actors. In general, CASBs should help you do this by providing a wide range of capabilities that protect your environment across the following pillars:
Visibility: Identify all cloud services, assign each a risk rating, and identify all third-party users and applications that can connect to the network.
Information security: identification and control of sensitive information (DLP) and respond to sensitivity labels in the content of the information.
Threat Protection: Offers Adaptive Access Control (AAC), provide user and entity behavior/habit analysis (UEBA), mitigate malware.
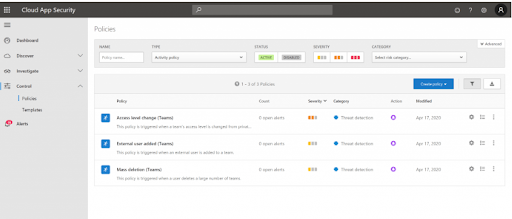
Compliance: Providing reports and dashboards to demonstrate cloud policies, assist in efforts to conform to database requirements and comply with Compliance regulations.
The framework/infrastructure of the Defender for cloud apps:
Discover and control the use of Shadow IT: Identify the cloud applications, IaaS and PaaS services used by your organization. Explore usage patterns, assess risk levels and business readiness of more than 25,000 SaaS applications against more than 80 risks. Start managing them to ensure security and compliance.
Protect your sensitive information anywhere in the cloud: understand, categorize, and protect sensitive information “at rest” exposure. Leverage built-in policies and automated processes to apply real-time controls across all your cloud applications.

Product capabilities
Protect against cyber threats and anomalies: Detect abnormal behavior in cloud applications to detect ransomware, compromised users, or rogue applications, analyze high-risk usage, and automatically remediate to limit risk to your organization.
Assess the compliance of your cloud applications: Assess whether your cloud applications meet relevant compliance requirements, including compliance with regulation and industry standards. Prevent data leaks to non-compliant apps and restrict access to regulated data.
YouCC Technologies, as a gold partner of Microsoft, has extensive experience in the management, maintenance, and implementation of Defender for cloud apps, or MCAS for SMB and ENT customers. We have years of experience with this product and accompany organizations in day-to-day operations of the system, solving problems and implementing the product.
So how can YouCC Technologies assist you and your organization?
- Architecture planning and implementation of information security solutions from a variety of security system manufacturers to the cloud.
- Implementation of Microsoft Azure Security and Microsoft 365 capabilities.
- Building a DevSecOps array, planning and implementing a security architecture in the world of the cloud and containers based on NGINX+.
- Implementing business solutions that allow technology to be an ENABLER for your organization.
- Developing end-to-end solutions in the cloud environment and bringing modern capabilities to the development environment.
- Proposing a managed model for the provision of services and solutions in the field of information technologies to be carried out in a regular and efficient manner.
Interested in your cloud security?
Looking for A company that will accompany you personally, professionally and without compromise? Let's talk!
Leave us your details so that we can get to know you, understand your needs and match you with the best service.
Strategic Partners



Technology Partners















Our Clients